|


Chapter 7
Contents
U.S.-PRC
Bilateral Agreement
Export
Licenses for PRC Launching of U.S. Satellites
Defense
Department Monitors
Country-to-Country
Agreements
Export
Licenses
U.S.-PRC
Technical Discussions Occur Prior to the Issuance of Export
Licenses
Technology
Transfer Control Plans and Security Plans Vary Throughout the Space
Industry
Temporary
Assignments of Defense Department Monitors Disrupt Continuity of Launch
Site Security
An
Inadequate Number of Defense Department Monitors Is Assigned to PRC
Launches
Uneven
Prior Technical Experience of
the Defense Department
Monitors
Inadequate
Headquarters Review of Monitor Reports
Lack
of Headquarters' Support
Lack
of Intermediate Sanction Authority
Conflicting
Industry Priorities
Satellite
Manufacturers, Not the Defense Department, Supervise Site Security
Personnel
Reliance
on Private Contractor Security Is Inadequate
Insufficient
Numbers of Security Guards at PRC Launche Sites
The
1999 Defense Authorization Act
Chapter 7
Summary

he U.S. satellite manufacturer is
responsible for the physical security of U.S. satellites that are exported
to the PRC, and for guarding against the unauthorized or illegal transfer
of U.S. technology during technical discussions that occur in the PRC.
The U.S. Government oversees this function by assigning a representative
of the Defense Technology Security Administration (DTSA), now known as the
Technology Security Directorate of the Defense Threat Reduction Agency, to
the launch site in the PRC.
This Defense Department "monitor" is responsible for ensuring that
the satellite manufacturer properly implements a Technology Transfer
Control Plan that is intended to provide and maintain protection
against the unauthorized transfer of U.S. technology. Defense Department
monitors also are required to attend all meetings of a technical nature
that may occur between the satellite manufacturer's employees and
representatives of the PRC launch provider leading up to and during the
launch.
In the course of their duties, Defense Department monitors are
required to report regularly to the U.S. Air Force's Space Command and
Technology Security Directorate Headquarters on their activities at
the launch site, including any security infractions they have detected.
According to the Director of the Defense Technology Security
Administration and Defense Department monitor reports, these infractions
represent instances that require the monitor's attention, but do not
necessarily constitute violations of the export license that should be
reported to the State Department. The guidance that is provided to Defense
Department monitors provides that, should they encounter a security
infraction at a launch site, they should first try to work out the problem
with the satellite manufacturer's personnel, including its security guard
force. If this effort does not result in resolution of the problem to the
satisfaction of the monitor, then the monitor is to call Headquarters and
advise a supervisor. The supervisor may then call the company to insist
that it remedy the security problem.
Defense Department monitors have reported many minor to severe
security infractions at launch sites in the PRC. While the Select
Committee's limited review has found no witness to confirm that a transfer
to the PRC of controlled U.S. technology has occurred as a result of
ineffective launch site security, given the difficulty of proving that an
improper transfer has occurred, it cannot be inferred that no such
transfer has taken place. Moreover, the security infractions that have
been documented demonstrate the potential for technology transfers to
occur. Testimony by the Department of Defense on the potential for a
technology transfer to occur as a result of access to a satellite in the
PRC provides a perspective for considering these security infractions.
The Defense Department concluded that visual or photographic access
to a satellite would allow confirmation of the existence of various
attributes of a satellite already in the public domain.
With additional, longer-term unguarded access, the Defense
Department estimated that a foreign intelligence collector could gain
physical access to the satellite and obtain technical information of value
regarding the satellite.
U.S. satellite manufacturers hire a security force to provide
physical security for a satellite while it is awaiting launch in the
PRC. In recent years, only one security guard company has bid on and
received contracts to provide this service in the PRC.
The conduct, professionalism, and abilities of that company's
personnel have been sharply criticized both by Defense Department
monitors and the satellite companies.
Because of the potential that technology transfers associated with
the launch of a U.S. satellite in the PRC can occur, it is critical that
the Defense Department monitors, the physical security guards, and the
satellite manufacturers provide effective protection of U.S. technology
associated with launches in the PRC. The Strom Thurmond National
Defense Authorization Act for FY 1999 has addressed several of the
criticisms received both from inside and outside the Defense Department
regarding its monitoring program. However, the Clinton administration has
not yet issued regulations to implement the Act.
Chapter 7
Text
PROTECTING
SENSITIVE
INFORMATION AT
PRC LAUNCH SITES

he United States relies on a variety of means to
protect controlled military-related technology during PRC launches of U.S.
satellites. These include bilateral agreements between the United States
and the PRC, export licenses for satellites and related technology, the
presence of private security guards at PRC launch sites, and monitoring of
launch-related activities and communications by U.S. Defense Department
representatives.
Background

U.S.-PRC
Bilateral Agreement
In 1988, prior to authorizing the first launches of U.S. satellites
from the PRC, the United States entered into a bilateral agreement with
the PRC to prevent unauthorized disclosures of controlled technology.
Under that agreement, the PRC agreed to give the United States access to
and complete control over the satellite and related information while it
is in the PRC for launch. The PRC also agreed not to seek to obtain
unauthorized information. 1
Export
Licenses for PRC Launching of U.S. Satellites
Under U.S. law (including the Arms Export Control Act, the
International Traffic in Arms Regulations, and regulations issued by the
Department of Commerce), 2 a private party wishing to launch a U.S.
satellite from the PRC must first obtain an export license to do so. The
license limits the access that the PRC can have to the satellite,
restricts the information that can be shared with the PRC, and requires
that the private party develop and abide by a plan to protect controlled
information from unauthorized disclosure. Private security guards are
often hired for this purpose.
Defense
Department Monitors
The United States requires that Defense Department representatives must
be present at the PRC launch site, and that the expense of these monitors
must be borne by the U.S. satellite manufacturer. These Defense Department
officials are responsible for overseeing the physical security of the
satellite and associated equipment and documents. They are also required
to monitor the technical interchange meetings that occur between U.S. and
PRC engineers throughout the satellite development and launch
campaign.
Each of these mechanisms for protecting sensitive, controlled U.S.
information from unauthorized disclosure is discussed in this chapter.
Unauthorized Access Allows
Opportunities
to Gain Information Concerning U.S. Satellites
and
Other Controlled Technology

Launch site security is intended to protect controlled military-related
technology, including information that could be gleaned from a U.S.
satellite and its associated documents, equipment, and technical
personnel, against disclosure to the PRC. Protecting controlled
information that might be stolen or inadvertently disclosed during the
launch or pre-launch period is a demanding and important task.
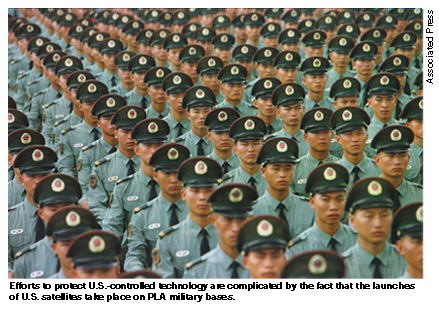
Efforts to protect U.S.-controlled technology during the launch and
pre-launch period in the PRC are complicated by several factors.
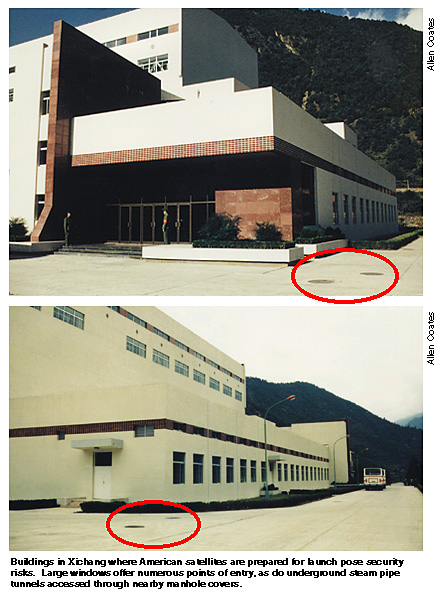
First, the launch and related pre-launch activities (often called the
"launch campaign") in the PRC take place largely on a PLA military base.
The Xichang Space Launch Center, from which many U.S.-manufactured
satellites are launched, is located within a PLA military installation.
Yet the U.S. satellite manufacturer is required to maintain control over
certain portions of the facilities and to make them secure during the time
a U.S. satellite and its associated documents and equipment are located
there.
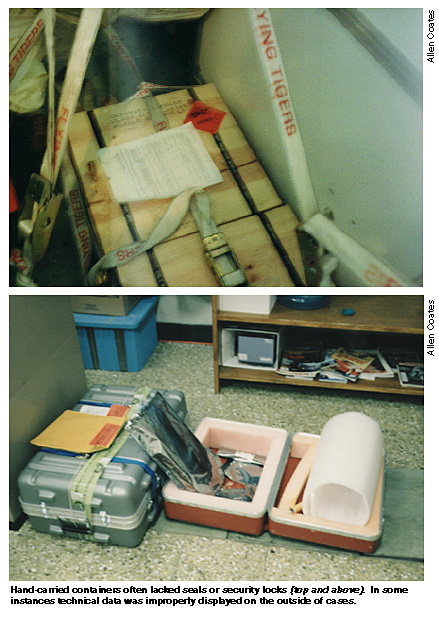
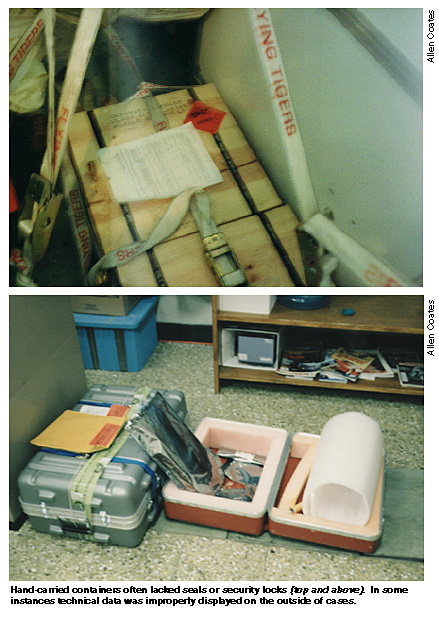
Second, U.S. satellite manufacturing companies take considerable
amounts of controlled equipment and technical data to the military
facility in order to assist them in their work to prepare the satellite
for launch. All this controlled information is required to be kept under
lock and seal when not in use and protected.
Yet PRC workers have legitimate reasons for having access to some of
these U.S. materials at various times, making the security function
particularly demanding.
Third, the U.S. engineers and support personnel who accompany the
satellite must live and operate far away from home, often under relatively
uncomfortable conditions. Some U.S. companies are unaccustomed to doing
business in such a demanding security environment.
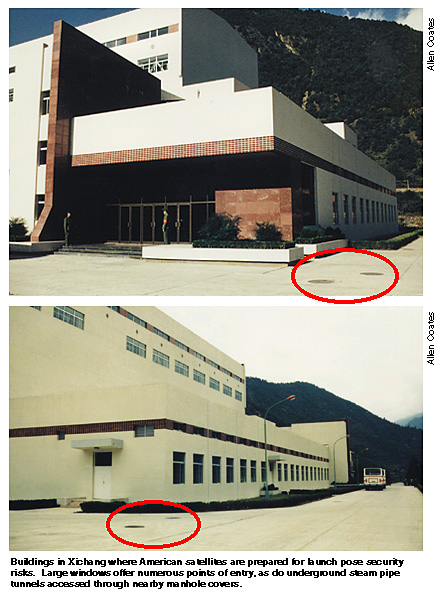
One satellite manufacturing company security official says that his
company takes every possible precaution, but notes that, if the PRC really
wanted to monitor everything that went on for the duration of the launch
campaign, it probably could easily do so.
The official also recalls that, during one launch campaign at Xichang
when building access badges were being made for local PRC personnel, a PRC
man gave the official a business card as identification. The card clearly
indicated the PRC man's title was "intelligence officer." 3 The individual
was not allowed access to the satellite.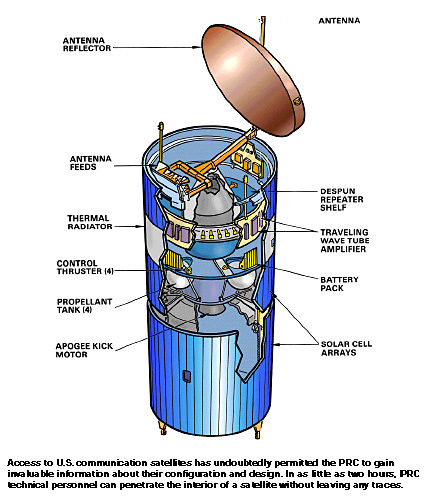
There are indications that the PRC carefully monitors the activities of
the U.S. personnel at the launch site. For example, Lockheed-Martin's
Director of Security explains that the power facility for the Xichang
Space Launch Center is located adjacent to the satellite processing
building. At one point when U.S. personnel supplied power to the satellite
for testing purposes, a number of PRC personnel emerged from the
facility's power building to determine what was happening. This was an
indication, in his view, of how closely the PRC was monitoring satellite
operations.4
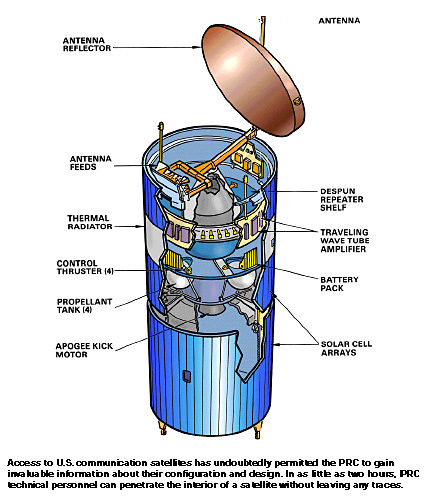
Access by the PRC to U.S.
communications satellites could permit the PRC to gain information about
the configuration and design of Western-manufactured satellites. If
the PRC has only visual or photographic access to a U.S. communications
satellite - the most common violation of U.S. security guidelines - only
information that confirms known capabilities and is already in the public
domain may be obtained. If the PRC had unrestricted access to a U.S.
communications satellite for at least two hours, the PRC military could
gain valuable information that is not otherwise available in the public
domain.
The PRC could accomplish even exploitation that penetrated the interior
of the satellite, given two hours of time, without leaving any traces.
With this kind of exploitation, the PRC could gain new information
about major satellite subsystems, as well as the design and manufacture of
each subsystem.
While unmonitored PRC access to a U.S. satellite for more than five or
six hours would produce diminishing returns, there is almost nothing about
a U.S. satellite that the PRC could not learn from unrestricted access for
24 hours.
Among the reasons the PRC would be interested in exploiting the
technology in U.S. communications satellites is to determine the satellite
manufacturer's techniques for passive thermal control. Thermal control is
critical to satellite life. The PRC would also likely be interested
in:
· Encryption
· The materials used in
satellites
· Engine and propellant
data
· Electrical design and
protection
Additionally, the PRC could seek to acquire information about the
dimensions and part numbers for satellite components or assemblies, as
well as dimensional tolerances. Obtaining part numbers could allow the PRC
to try to acquire U.S. technology directly from the manufacturer that
would improve the performance and provide for longer on-orbit life for PRC
satellites.
Launch-related equipment, documents, and personnel accompany the
satellite to the PRC military facility for the launch campaign. Technical
interchange meetings between U.S. and PRC experts also occur. All of these
materials and exchanges relating to controlled technology or information
are required to be monitored by the Defense Department.
Unauthorized PRC access to controlled equipment or materials, including
blueprints or testing equipment, could benefit the PRC's own military
space launch activities.
Unauthorized PRC participation in technical discussions, as well as PRC
eavesdropping into technical discussions among U.S. experts, could have
similar military benefits to the PRC. For example, the chapters of this
Report concerning Loral and Hughes discuss in detail the potential gains
to the PRC from technical discussions held in connection with unauthorized
failure analyses performed by these companies' experts.
Inadequacy of Current Safeguards

The Select Committee's
investigation has identified numerous security lapses in connection
with U.S. satellite launches in the PRC that could have provided the
opportunity for improper transfers of controlled information.
U.S. policy permitting the launch of U.S. satellites from the PRC rests
in large measure on the assumption that companies will comply with legal
requirements governing controlled information, and that such information
will not be transferred to the PRC during a launch campaign. However, as
noted below, reporting available to the Select Committee indicates that
there have been lapses in security.
There is also reason to believe that not all lapses in security may
have been reported. During the course of the Select Committee's
investigation, no witness has been found to confirm that a transfer to the
PRC of controlled technology has occurred as a result of ineffective
launch site security. However, given the difficulty of proving that an
improper transfer has occurred, it cannot be inferred that no such
transfer has taken place.
Security lapses reported by the Defense Department at a number of
launches in the PRC include the following:5
· A PRC national set up all
secured and unsecured fax, voice and data communications for a U.S.
satellite
manufacturing company at the PRC launch site
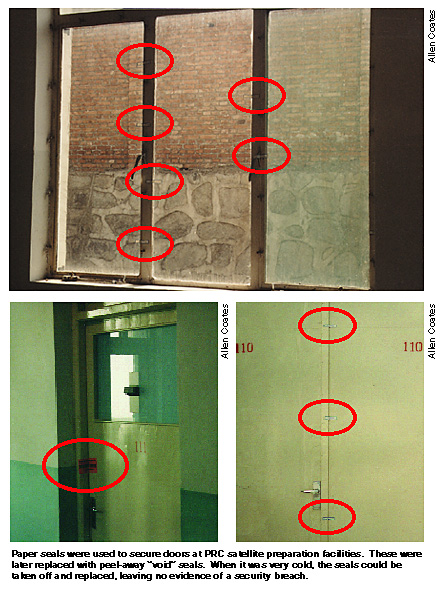
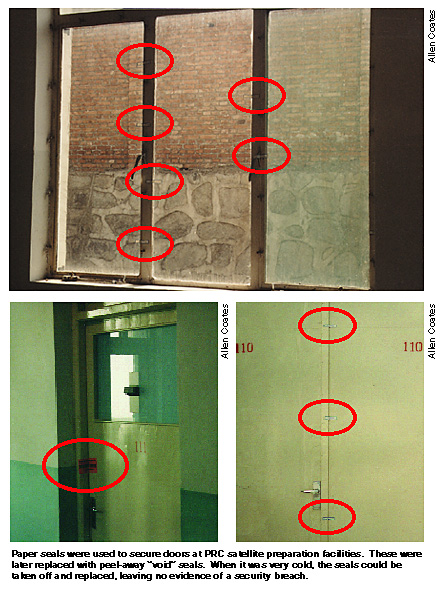
· Doors, windows or equipment
unsealed or unattended
· Unsecured windows - in one
instance a window may have been unsecured for 21 days
· Multiple instances of
equipment left unattended
· Doors discovered with seals
ripped off
· Controlled documents missing
or unattended
· A laptop computer containing
digital pictures of the satellite left unattended in a hotel
room
· Notebooks containing
controlled information left unattended in areas where the PRC had
access
· Filing cabinets containing
controlled documents left open or without proper seals
· Documents improperly removed
from cabinets
· Controlled equipment
improperly discarded in trash
· Multiple examples of
documents shipped without proper locks/seals
· Satellite test data left in
cabinets without seals
· Satellite diagrams and other
sensitive documents left out in the open
· Schematic of satellite bus
equipment module and related documents left out
· Test valve document left
out
· X-ray position diagrams found
in improper location
· Notes left on
blackboards
· Improper access by PRC
workers
· PRC workers spent long
periods of time (an hour or more) in areas where they were not supposed
to be present
· No access list of PRC
personnel provided to monitor
· PRC workers in controlled
areas without proper escorts or badges
· PRC technicians worked
unsupervised in the area of the satellite
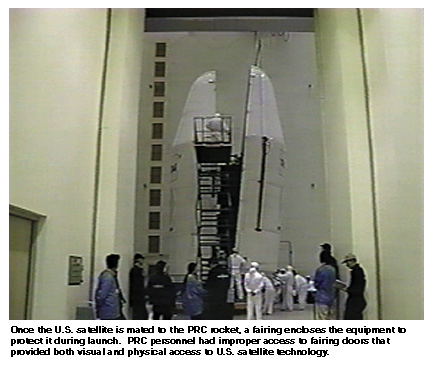
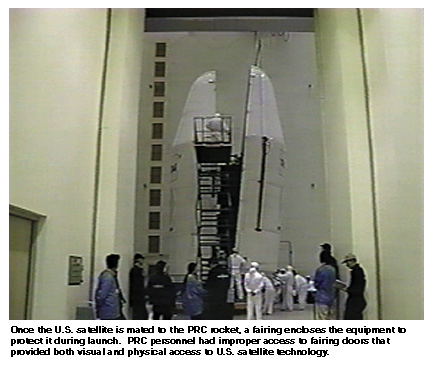
· PRC personnel had improper
access to fairing doors that provided visual/physical access to the
satellite
· Unauthorized photographs were
taken of the satellite
· Controlled information not
properly inventoried
· Telephones used without
proper security procedures
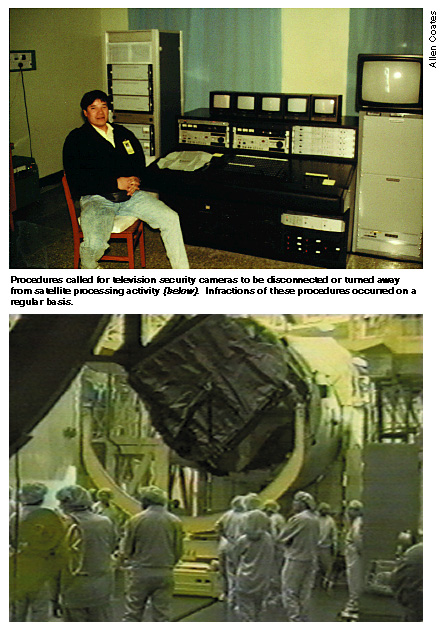
· Improper practices with
security cameras
· Security cameras
mis-positioned, giving the PRC potential access to the satellite
container without detection
· Failure to man proper
location when security camera inoperable
· Lax attitudes toward security
exhibited by U.S. personnel, including failures to record or investigate
potential violations
· Blueprints of Vandenberg Air
Force Base facilities exposed in the presence of PRC personnel
· Unauthorized discussions with
PRC personnel
Defense Technology Security Administration Director Tarbell confirms
that Defense Department monitors have provided reports that there had been
circumstances of short-duration, unescorted PRC access to U.S.
communications satellites in the PRC.6 However, Tarbell says that he is
not aware of any evidence that this access resulted in a technology
transfer that would significantly affect national security.7
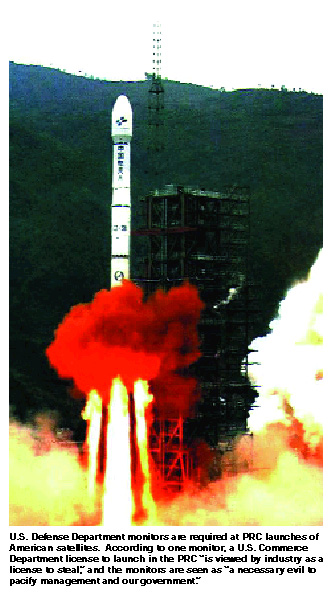
A Defense Department monitor wrote the following comments in his final
report during a 1998 PRC launch campaign:
This assignment for DTSA [the Defense Technology Security
Administration] has proven to be exceptionally taxing and difficult. We
are trained, given the necessary tools/skills and expected to protect
U.S. technology from improper disclosure/compromise.
Our responsibilities as monitors become transparent when aerospace
companies (some not all) are given a Commerce License. It is viewed by
industry as a license to steal and the monitors are a necessary evil to
pacify management and our government.
There is a general consensus within the public sector that, if
restrictive measures and significant penalties are not levied against
industries (specifically aerospace) by the Commerce Department (or
higher), our technology will be compromised to such a staggering level
and that our highest level of technology advancements will be available
to our international competitors before it comes off the research and
development floor.
We as a nation cannot allow or afford to have industry police
itself when it comes to national security . . .
History is filled with unnecessary shortcuts in
safeguard/
security procedures resulting in the loss of American
lives and federal grand jury investigations into illegal transfer of our
technology by major corporations in an effort to increase their profit .
. .8
In an October 27, 1992 memorandum, Sumner Benson, Director of the
Defense Technology Security Administration Technology Policy Directorate,
expressed the following concerns regarding the security situation relating
to the launch in the PRC of the FREJA satellite:
During the subject launch campaign, PRC personnel had unmonitored
access to the FREJA satellite after it had been mated with the PRC LM2C
launch vehicle [Long March 2C rocket]. Because PRC access was
unmonitored, the [Defense Department] technology security monitors
cannot state with certainty that no technology was transferred.
During a three day period from 26-28 September 1992,
the
[Defense Department] representatives noted PRC activity in the Vehicle
Equipment Bay (VEB), located in the lower section of the FREJA clean
room at the top of the LM2C [Long March 2C] booster.
Neither the [Defense Department] representatives nor the Swedish
Space Corporation (SSC) representatives [the
purchaser of the
satellite] had been informed about this activity, and it had not been
included in Combined Operations Procedures. The PRC were apparently
working on their
navigation and guidance equipment, but access to
the lower side of the FREJA satellite was possible from the VEB.
When the [Defense Department] representative became aware of and
attempted to monitor this activity, he was prevented from doing so by
the PRC launch site commander.
Through a series of meetings with PRC representatives of the
launch site, the launch site parent organization (CLTC) and PRC Defense
Department (COSTIND), the [U.S. Defense Department] representative
determined that the PRC:
Did not believe that unilateral work on their equipment
was
combined operations activity and therefore advanced
notification and
monitoring was not required;
Felt that the [Defense Department] monitor was overzealous in
wanting to monitor the PRC activity in the VEB;
Did not feel monitoring was necessary because they [the PRC] could
be trusted not to try to acquire any technology even when they had
access to the satellite; and finally,
Felt that they [the PRC] had not violated the Technology
Safeguards Agreement. 9
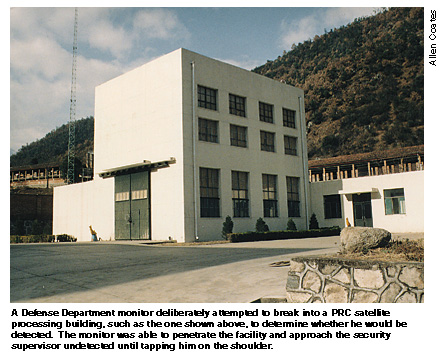
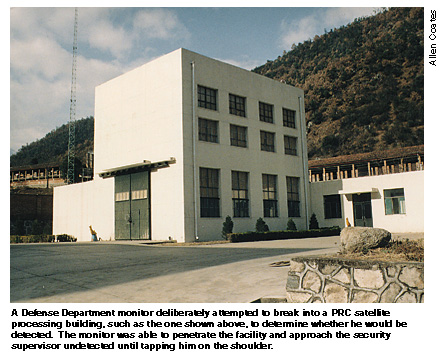
In another instance, a Defense Department monitor indicated that he
deliberately attempted to break into the satellite processing building in
the PRC to determine whether he would be detected. The monitor was able to
penetrate the facility and approach the security supervisor undetected
until tapping him on the shoulder. 10
Safeguarding U.S.-Built Satellites
and
U.S. Rocket Technology at PRC Launches

Country-to-Country Agreements
In 1988, and again in 1993, the United States entered into agreements
with the PRC for the purpose of precluding the unauthorized transfer of
sensitive technology associated with the export of U.S.-manufactured
satellites for launches in the PRC.
The agreements specify that at no time will there be unmonitored or
unescorted access by PRC nationals to any of the equipment or associated
technical data.11 Additionally, only "form, fit and function data" 12 that
describe mechanical and electrical mating requirements for attaching the
satellite to the rocket are authorized for release to PRC nationals.13 The
agreements further indicate that the U.S. Government shall oversee and
monitor implementation of Technology Transfer Control Plans, which are
required to be developed by the satellite manufacturer. The PRC is
required to permit and facilitate that monitoring.
Access to all satellite equipment and technical data is required to be
controlled on a 24-hour basis by U.S. persons who have received training
in security procedures from the U.S. Government. These U.S. persons must
exercise this control throughout launch preparations, satellite
transportation, mating/demating, test and checkout, satellite launch, and
required return of equipment to the United States. 14
Export
Licenses
With the passage of the Strom Thurmond National Defense Authorization
Act for Fiscal Year 1999, all satellites and related items have been
transferred to the United States Munitions List, and their export is
controlled by the State Department under the Arms Export Control
Act.15
Prior to this Act, the Department of Commerce had jurisdiction for
licensing the export of some commercial satellites from 1993 through 1996,
and over export licenses for all commercial satellites from 1996 through
1998.16
During the period 1993 through
1996, the Department of Commerce issued three export licenses for
commercial communications satellites to be launched in the PRC that did
not require the presence of Defense Department monitors, and did not
require the U.S. exporter to reimburse the Defense Department for the
expenses of providing monitoring in the PRC.17
Although the U.S. licenses routinely stipulate the presence of a
Defense Department monitor, this requirement has not always been
well-received by the satellite manufacturer.
For example, in one instance, a satellite manufacturing company
demonstrated a negative attitude toward the presence of a Defense
Department monitor as required under a license issued by the Department of
Commerce. The Defense Department monitor explained that he had a
disagreement with a program manager and the company site security
supervisor over the manner in which a computer board would be shipped. The
security site supervisor told the monitor that his company had a
Department of Commerce license for that particular satellite launch and,
therefore, the Defense Department monitor was in the PRC as a
courtesy.18
Licenses issued by the Department of State include detailed provisos
concerning technology transfer and security. For example, one license
issued to Hughes stipulated:
Hughes must develop a plan(s) to comply with the applicable
provisos of this [license]. These plans must address the technology
safeguards implementation, security support, tranportation, debris
recovery and other issues. 19
The Defense Department's Responsibilities
for
Safeguarding U.S. Technology at Launches

The Defense Department provides oversight in safeguarding technology at
launch sites in the PRC. The Defense Department does this in part by
overseeing implementation of Technology Transfer Control Plans and
Security Plans prepared by the U.S. satellite manufacturers as required
under export licenses.
The Defense Department also is responsible for monitoring all technical
interchange meetings between U.S. and PRC personnel. 20 These meetings can
occur as early as two years prior to a launch and continue during the
launch campaign, as well as after a launch. Provisos in the U.S. export
license for the PRC indicate the limits of the technical data that may be
exchanged in these meetings. A Defense Department monitor is required to
attend technical interchange meetings when PRC nationals are in attendance
in order to assure that only data permissible under the license is
exchanged.
Deficiencies Observed in the Current
System

U.S.-PRC
Technical Discussions Occur Prior to
The Issuance of Export
Licenses
When a U.S. satellite manufacturer applies for an export license for
the satellite and related technical data, the Department of State or the
Department of Commerce notifies the Defense Department that monitors will
be needed to oversee the launch and the technical interchange meetings.
However, technical discussions are conducted over the telephone or through
informal personal discussions and marketing meetings prior to the license
being issued.
This illustrates the fact that U.S. satellite manufacturers are on the
honor system, to a large extent, in ensuring that no licensable technical
data is exchanged in the absence of a Defense Department monitor.21
Although Defense Technology Security Administration Director David
Tarbell agrees that "anything is possible," he believes it is not likely
that a technology transfer would occur during early contractual
discussions of this type. Tarbell says that conversations in these early
stages would relate to the type of satellite the buyer wants, not how the
satellite would be launched.22
Technology
Transfer Control Plans and Security Plans Vary Throughout the Space
Industry
The current U.S. Government export control system requires industry to
formulate a variety of required plans, including Technology Transfer
Control Plans and Security Plans. These plans are provided to the Defense
Department for review and approval. However, the plans vary from company
to company, despite the fact that the launch facilities are the same, and
the processing procedures of each company are similar.
Tarbell comments that, although standardization of the plans would be
desirable, some degree of flexibility should be allowed, and any
standardization should not rise to the level of rulemaking. 23
Temporary
Assignments of Defense Department Monitors Disrupt Continuity of Launch
Site Security
Because the Defense Department did not have the resources to allow its
permanent staff to participate as monitors on a regular basis, the Defense
Technology Security Administration decided that the monitors for
communications satellite launch campaigns in the PRC and U.S.-PRC
technical interchange meetings should be drawn from the Air Force Space
Command.24 According to one former Defense Department official, an
individual often is chosen to be a monitor by Space Command because he or
she is between jobs or may be expendable.25
The duration and living conditions of these assignments make them even
more unappealing. In addition, these assignments are unpopular with
commanding officers because they do not enhance the Space Command mission,
and because participation by their personnel could be construed as
indicating that they have excess resources at their disposal.
The lack of a permanent corps of Defense Department monitors with
relevant technical experience has drawn criticism from the space
industry.26
An aggravating circumstance is the frequent rotation of monitors
throughout the launch campaign. During the five-to-eight week duration of
one PRC launch, for example, as many as five monitors were rotated in and
out of the site. 27 Additional monitors may have participated in technical
interchange meetings that occurred prior to the launch.28
Frequent rotation results in a
lack of continuity and consistency in monitoring decisions during the
technical interchange meetings and the launch. The information discussed
during a technical interchange meeting is often based on the information
discussed during a preceding meeting.
Thus, a new monitor coming
into a meeting without having attended the previous meeting is not aware
of what particular information the previous monitor may have either
prohibited or allowed the participants to discuss. Additionally, as one
former Defense Department monitor opined, "The knowledge base that's
required from one technical meeting to the other sets the precedents for
the next one." 29
The same is true at the launch site. A series of Defense Department
monitors coming and going disrupts continuity. According to one security
official, ". . . to have three different DTSA [Defense Department]
representatives is very difficult from a security perspective because . .
. they each have their own areas of specialty, they each have their own
background and limited experience." 30
For example, while the first Defense Department monitor assigned to the
launch when the satellite arrives in the PRC is responsible for ensuring
that the facility is secure, in one instance a replacement monitor toured
the facility and made a series of changes to the physical security plan
that had been found to be satisfactory by the
previous monitor.31
An Inadequate
Number of Defense Department Monitors Is Assigned to PRC
Launches
While the number of Defense Department monitors assigned to a launch
site has varied over the years, it has been standard practice to assign
only one or two monitors at a time to launches in the PRC.
However, a July 1993 order of the Secretary of the Air Force directed
that:
Air Force Space Command will identify two to five qualified
technology safeguard monitors for each satellite program, depending on
the program's scope, complexity and duration.
Further, for each launch campaign (typically five to eight weeks),
Space Command will ensure that two to four monitors are present at
the launch site at all times.
To accomplish this, Space Command will assign one lead
monitor
to remain at the foreign launch base for the duration of the mission,
and will typically form two teams of two monitors each to accompany the
lead monitor. Each team of two will be at the foreign launch site for
about five weeks, (nominally), plus a week of travel time for each team
(counting both legs of the trip).32 [Emphasis added]
Some company representatives
believe that one Defense Department monitor is adequate during the
course of a normal launch campaign to cover technical interchange meetings
and to monitor technology at the site. This, they say, is largely because
most of the technical discussions have already occurred during the years
leading up to the launch. One company's security manager says meetings
with the PRC at a launch never would occur without the presence of the
Defense Department monitor.33 In the event of a launch failure, however,
more monitors may be necessary.
The sole Defense Department monitor at the Intelsat 708 failure had
difficulty working alone to oversee interactions between the PRC, Loral
employees, and the private security force to ensure that no technology
would be transferred as a result of the failure. The monitor recalls
that:
Following the destruction of the Long March 3B, Loral upper
management completely took over the operation of satellite piece
recovery and ignored my advice to delay piece recovery until the area
became safe and a meeting between PRC, Loral and myself could control
the situation.
As a result, at least two technicians returned from the crash site
complaining of bulging eyes and severe headache requiring a
5-minute
oxygen treatment.
I believe we were lucky we recovered 63.5 percent of the vehicle
[rocket] along with the [satellite's] encryption-decryption
equipment.34
This same monitor says he was not able to keep the Loral program
manager from traveling to the crash site unaccompanied before the site was
declared safe.35
Uneven Prior
Technical Experience Of
the Defense Department Monitors
Without a permanently assigned corps of Defense Department monitors,
matching the experience of the monitor to the necessary tasks is
difficult. Program officers, instead of engineers, have been used as
monitors.36
Some company personnel noted that the Defense Department monitors have
different backgrounds, and their technical expertise, therefore, varies.37
By and large, the security managers interviewed by the Select Committee
believed that the Defense Department monitors had the necessary technical
expertise to keep pace with discussions between the company engineers and
the PRC. 38
The space industry has indicated that the Defense Department should
maintain an adequate staff of trained professionals in monitoring
technology transfer at foreign launches, with the end result being more
uniformity overall.39
The Defense Department monitors participate in a three-day training
course to prepare for assignments. The training is conducted by Air Force
Space Command and includes such topics as the International Traffic in
Arms Regulations, Export Administration Regulations, Memorandums of
Agreement, Licensing Provisos, Technology Transfer Control Plans, Security
Plans, Daily Logs, Incident Reports and Trip Reports.40 Training also
includes formal briefings by the Defense Department, and continues on an
ad hoc basis with regard to particular licenses.41 As launch numbers have
increased, there have been more training sessions that incorporate lessons
learned during past launches to prepare monitors for future assignments.
42
Inadequate
Headquarters Review of Monitor Reports
The July 1993 order of the Secretary of the Air Force directed that the
lead Defense Department monitor for each launch campaign must maintain a
complete daily log of events during that campaign. This daily log must
include records of each meeting between the U.S. satellite manufacturer
and the foreign launch provider, and it must summarize all decisions
affecting technology security.43
The monitors are instructed to fax their daily logs to both Space
Command and the Defense Technology Security Administration (now the
Technology Security Directorate).44 Because the fax machines often are not
reliable at PRC launch sites, Space Command also faxes the monitor logs to
the Defense Technology Security Administration to ensure that they are
received.45
The lead Defense Department monitor is required to report the satellite
processing status and plans, along with any safeguarding problems and
recommendations, to the Defense Technology Security Administration (now
the Technology Security Directorate), and also to Space Command at least
once a week during a launch campaign.46
Space Command is responsible for the receipt and storage of reports
that the Defense Department monitors prepare and send while they are on
assignment at a launch site abroad. 47
The Director of the Defense
Technology Security Administration, David Tarbell, says he is not aware
whether Defense Department monitors' reports are first received at his
agency and reviewed, or whether they are sent directly to Space
Command prior to being warehoused there.48
Although Space Command schedules the monitors and is considered to be a
flow-through point for reports from the monitors, Space Command's
interaction with the monitors is administrative, not substantive, and
similar to that of a program manager. Yet, Space Command receives daily
activity logs from Defense Department monitors that contain information
concerning security incidents and infractions at the launch site.49
Tarbell stressed that it is the Defense Department monitor's
responsibility to assure that serious incidents are brought directly to
Headquarters' attention.50 Less significant security infractions are
reported to both Space Command and the Defense Technology Security
Administration via the monitor's daily logs.
Actual entries from Defense Department monitors' logs appear at the end
of this chapter.
According to Defense Technology Security Administration officials, only
two security matters reported by Defense Department monitors have been
raised to the attention of the Director in the past 13 months. 51
Lack of
Headquarters' Support
Some Defense Department monitors have reported difficulties in
contacting Defense Technology Security Administration management in the
United States while they are on a PRC launch campaign.
One Defense Department monitor noted in his daily log, during a PRC
launch operation in 1998: ". . . Attempted to contact the DTSA office in
Washington, however, all personnel were TDY [away on temporary duty]."
52
Another Defense Department monitor also attempted to contact the
Defense Technology Security Administration in Washington on another date,
and also was told all personnel were away on temporary assignments. 53
The Defense Department monitor assigned to the Loral-Intelsat 708
launch in the PRC reports that he attempted unsuccessfully to resolve
repetitive security infractions during that launch. He indicated that he
then attempted to contact Space Command in Colorado, and wrote several
memoranda to his superiors at the Defense Technology Security
Administration. 54 That official then had to telephone Loral directly to
have the deficiencies reviewed and corrected.55 Following the phone call,
the Defense Department monitor acknowledged security had "greatly
improved." 56
The Loral site security supervisor for the Intelsat 708 launch
indicates that the Defense Technology Security Administration did not
support the monitor in attendance at that launch. The monitor reportedly
had no security plans provided to him by the agency beforehand, and had to
make on-the-spot decisions concerning the release of documents.57
Lack of
Intermediate Sanction Authority
One Defense Department monitor explains that several types of security
violations can occur during a launch campaign or a technical interchange
meeting.58 Most incidents fall into the category of infractions that do
not rise to the level of a license violation, but may include such things
as controlled documents being left out in the open, unescorted visitors,
and broken security seals on doors or windows.
Tarbell characterized infractions as instances that run the gamut "from
very, very minor things to things that require DTSA's attention, but don't
rise to the level of an export control violation that we should report to
the State Department." 59 Tarbell says that Defense Technology Security
Administration guidance to monitors encourages them to try to resolve
problems on site and, if that is not effective, to contact the agency
immediately so that it can resolve the situation with the company.60
Tarbell says that he believes that his agency has a significant
sanction available - the ability to stop a launch. In addition, Tarbell
also indicates that he believes that the Defense Technology Security
Administration has additional enforcement powers by virtue of its
relationship to the licensing process and the Arms Export Control Act.
However, there appear to be no intermediate sanctions available to
discourage relatively common, repetitive security infractions.
Conflicting
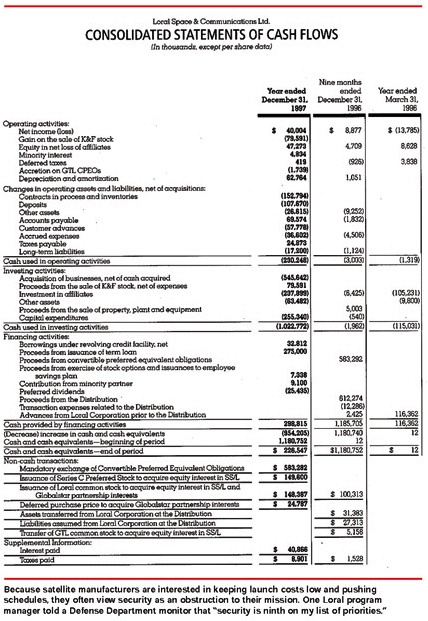
Industry Priorities
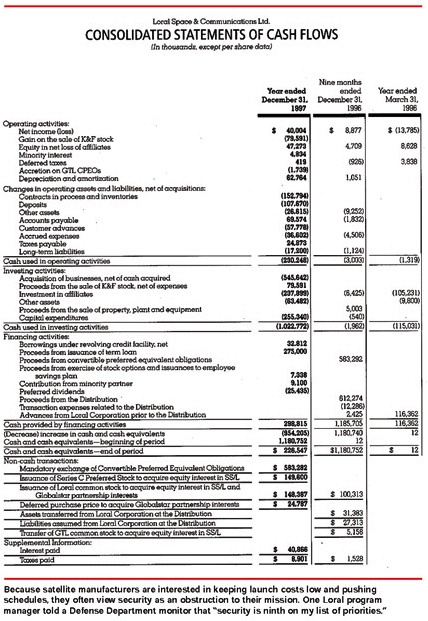
Tarbell acknowledges that the satellite manufacturer's program
management staff is interested in pushing the schedule, making sure costs
are low, finishing the project, and limiting risk to the project. This
forces the satellite firm to make judgments that push as hard as possible
against the barriers of security and technology transfer. This is why, in
Tarbell's view, Defense Department monitors are necessary. 61
One Loral site security manager indicates that industry project
managers consider security to be an obstruction to the completion of their
mission. It is an extra cost and poses additional obstacles to them.62 One
Loral program manager repeatedly stated to a monitor that "Security was
ninth on my list of priorities." 63
A former security manager for Loral says that he argued against having
the program manager being placed in charge of satellite security during
the Intelsat 708 launch in the PRC, because a program manager's main
objective of launching the satellite will take precedence over security.64
He was overruled twice, even after several reports were received during
the launch campaign that the Defense Department monitor was having
problems with the program manager's lax attitude toward security
issues.65
During the Loral-Intelsat 708 launch campaign, complaints were made
that the program manager invited PRC nationals into the satellite
processing building and allowed them to be photographed standing in front
of the satellite.66 The PRC nationals were alleged to be employees of the
local hotel, as well as members of the PRC technical team.67 Comments were
made that the program manager's Chinese heritage invoked his sense of pity
concerning the quality of life of the PRC nationals near the launch site,
and motivated him to invite the visitors for a photo session.68 No record
of this incident appears in Defense Technology Security Administration
files.
Satellite
Manufacturers, Not the Defense Department,
Supervise Site Security
Personnel
At the launch site, the security force reports to the U.S. satellite
manufacturer's representatives (because the security personnel's
contractual obligations run to the company that pays them, not to the U.S.
Government). Therefore, the security force cannot be considered to
constitute an independent security function.69 Yet some industry officials
insist that the program manager should be responsible for the entire
launch campaign, including security.70
Reliance on
Private Contractor Security Is Inadequate
United States commercial satellite manufacturers routinely contract
with a private security firm to provide security, including protection
against technology transfers, at PRC launch sites. Since few, if any,
other security firms currently provide this specialized service, Pinkerton
Aerospace Division has been used almost exclusively by U.S. satellite
firms launching in the PRC. Of the ten security firms identified in a
recent business journal, for example, only Pinkerton currently offers
foreign launch site security services. 71 Another firm, Launch Security
Services International, provided such services prior to going out of
business in 1996.72
Both the Defense Department monitors and industry representatives have
complained about the quality of work and the conduct of some members of
the contractor security forces.73
One Defense Department monitor experienced a range of problems with the
private security guard force on a PRC launch, including:
· Sleeping on the job
· Reporting to work under the
influence of alcohol
· Poor reporting on daily logs
and at shift changes
· Racial and gender slurs
towards PRC nationals in the local village
· Routine bus trips into the
town to meet prostitutes
· Overall lack of respect for
management
The Defense Department monitor
indicates that the solicitation of prostitutes became so intense that
he was approached by a PRC foreign affairs officer who was assigned to the
launch to report that one of the guards had been seen soliciting
prostitution in front of the local police department.74
One security guard even reported for duty carrying a sleeping
bag.75
Another Defense Department monitor describes a situation during a
launch campaign in the PRC in which the contractor security guards moved a
table out of the line of sight of a video surveillance camera, in order to
use it as a bed.
Since the table on which the security guard was sleeping also
obstructed entry and exit to the room, the Defense Department monitor
called the guard on the telephone to request that the table be moved away
from the door, and back into the position where it had previously been
located.
The guard reportedly responded that he was "not in the furniture moving
business." 76 In response, the Defense Department monitor had to leave his
duties and walk to the remote building to confront the guard and ensure
that the table was moved.
Insufficient
Numbers of Security Guards at PRC Launch Sites
Each U.S. satellite manufacturer is permitted to develop its own
security plans for launches in the PRC, with subsequent approval by the
Defense Department. As a result, the number of security guards at PRC
launch sites varies.
One U.S. satellite company security official indicates he believes that
attempting to take less than ten contract security guards to a launch in
the PRC is "rolling the dice" in terms of the ability to provide effective
safeguards. Taking less than nine is, in his view, "crazy." Most satellite
manufacturers take 12 or 13 security officers to a PRC launch.77
However, one Loral site security supervisor says he was asked by the
program manager to try to reduce costs and investigate the possibility of
reducing the number of contractor security staff, since the program
manager had observed that security guards often were idle. The supervisor
agreed to require only nine security officers - even though he had never
been to the PRC launch site, and even though he was aware that 12 security
guards had been used at the same facility for the previous Loral launch.
The Loral site security supervisor says that he experienced no problems
maintaining proper security with only nine officers.78
Some satellite manufacturers attempt to augment the contractor security
force by using their own technical staff to provide escorts for nationals
during a launch campaign. During launches in the PRC, this has resulted in
periods when PRC visitors were unescorted and unattended, because the
technicians were called away or not attentive to their escort duties.
79
Correcting Security Deficiencies

In recent months, an effort has been underway to standardize security
practices among U.S. companies launching satellites in the PRC. Security
managers from Hughes and Loral have been trying to form a working group
with the Defense Department "to try to standardize . . . some of our
practices." 80
Tarbell notes that U.S. satellite companies have expressed great
interest in working with the Defense Department to achieve some
standardization in their approaches to site security.81
Additionally, some companies hold "lessons learned" sessions after a
launch occurs to incorporate circumstances and responses encountered
during a launch, including site security, into future launch
operations.
Following the failure of the Intelsat 708 launch, for example, the
security manager reviewed the Defense Department's reports and findings
and made changes to the company's security system. He concluded that Loral
needed "a much more intensive educational program to inform everybody that
there will be a very stringent document control system with bright red
covers and locked safes and daily inventories.82 Additionally, the Loral
security manager requested that a representative from the Defense
Department speak to company management to discuss how the company could
improve its security procedures.
The 1999
Defense Authorization Act
The Strom Thurmond National Defense Authorization Act for Fiscal Year
1999 provides that U.S. business interests must not be placed above U.S.
national security interests, and that the export or transfer of advanced
communication satellites and related technologies from U.S. sources to
foreign recipients should not increase the risks to the national
security.
Further, the Act states that the United States should not export
missile equipment or technology to the PRC that would improve its missile
or space launch capabilities, and should pursue policies that protect and
enhance the U.S. space launch industry.
In furtherance of these interests, the Act calls for mandatory Defense
Department monitors and reimbursement of related costs by the U.S.
satellite manufacturer, in any case in which a license is approved for the
export of a satellite for launch in a foreign country. The stated purpose
is to prevent the unauthorized transfer of technology, including technical
assistance and technical data. 83
The Secretary of Defense is also directed by the Act to establish a
program for recruiting, training and maintaining a staff dedicated to
monitoring launches of satellites in foreign countries. The Act calls for
mandatory Technology Transfer Control Plans approved by the Defense
Department, and Encryption Technology Transfer Control Plans approved by
the National Security Agency.84
The Technology Security Directorate within the Defense Department's
Defense Threat Reduction Agency is developing plans for implementation of
the Act. Tarbell indicated that the plans are undergoing funding review
within the Defense Department. Tarbell also indicated that the Technology
Security Directorate is reviewing the range of satellite-related
activities in which it should be involved. 85 |